Quick Summary: Predictive analytics in cybersecurity uses historical data, machine learning, and statistical modeling to forecast potential cyber threats before they materialize. This proactive approach enables organizations to identify attack patterns, prioritize vulnerabilities, and deploy defenses ahead of incidents rather than reacting after breaches occur.
Cybersecurity professionals spend too much time putting out fires. Traditional security methods wait for something bad to happen, then scramble to contain the damage. That reactive approach made sense fifteen years ago, but threat actors have evolved.
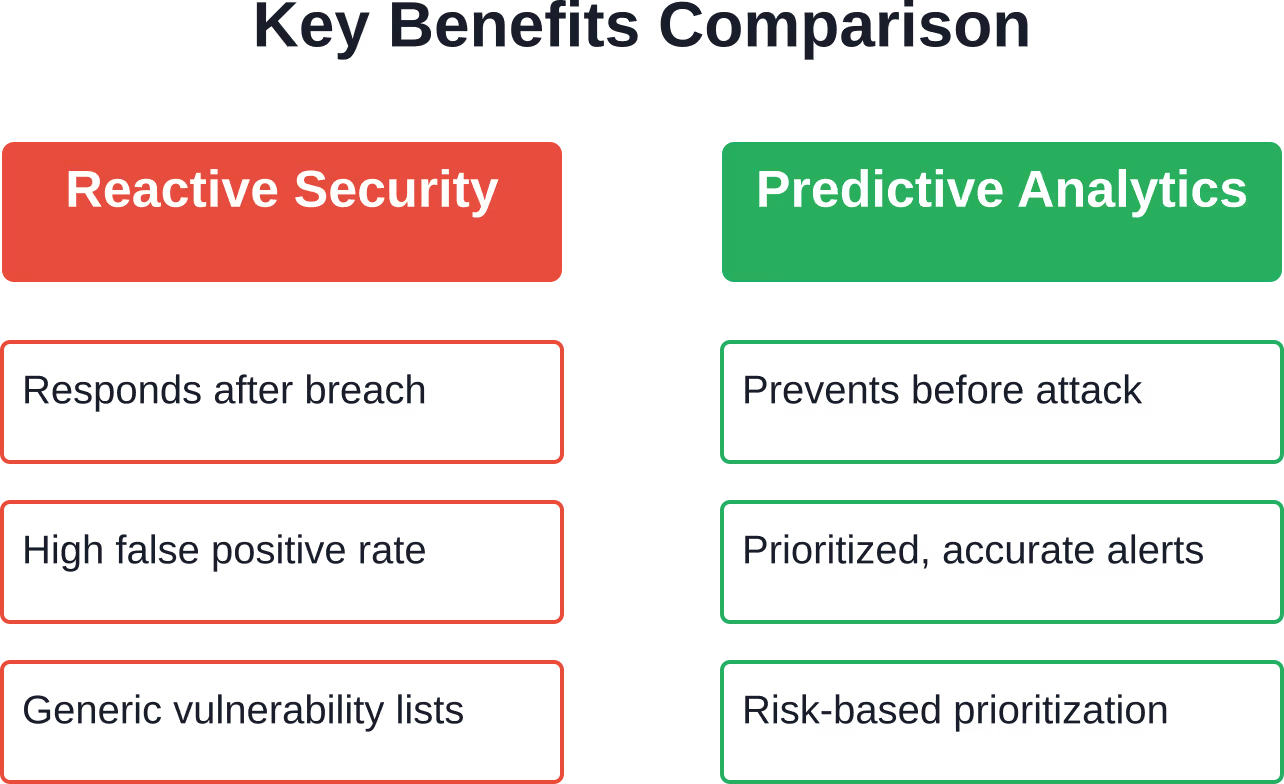
Predictive analytics flips that script entirely. Instead of waiting for intrusions and patching vulnerabilities after detection, security teams can now forecast which attacks are likely to target their systems and shore up defenses before threat actors strike.
The shift from reactive to proactive defense isn’t just theoretical. Organizations using predictive threat analytics spot anomalies before they escalate into incidents, help security teams prioritize high-risk alerts, and reduce false positives that waste analyst time.
What Predictive Analytics Actually Means in Cybersecurity
Predictive analytics applies statistical techniques to current and historical data to forecast future events. In the cybersecurity context, that means analyzing past attack patterns, user behavior, network traffic, and system logs to identify indicators that precede security incidents.
The foundation rests on three core components: data collection, pattern recognition, and forecasting models. Security systems gather massive volumes of data from firewalls, endpoint devices, authentication logs, and threat intelligence feeds. Machine learning algorithms then parse that information to identify patterns that correlate with specific threat types.
Here’s the thing though—predictive analytics isn’t about crystal balls or perfect foresight. The goal is probability, not certainty. These systems calculate likelihood scores that help security teams allocate limited resources to the most pressing vulnerabilities.
How Machine Learning Powers Threat Prediction
Machine learning algorithms form the engine behind modern predictive analytics. These models train on historical security data to recognize normal baseline behavior, then flag deviations that suggest potential threats.
Supervised learning models learn from labeled datasets where previous incidents are tagged and categorized. The algorithm identifies features that distinguished those incidents from routine activity, then applies those lessons to new data streams.
Unsupervised learning takes a different approach. Without pre-labeled examples, these algorithms cluster data points based on similarity and detect outliers that don’t fit established patterns. That’s particularly useful for identifying zero-day exploits that don’t match known attack signatures.

Apply Predictive Analytics with AI Superior
AI Superior builds predictive models that help analyze security data and detect patterns linked to potential threats. The focus is on integrating these models into existing systems so they support monitoring and response in real time.
They begin with data assessment, build a working model, and integrate it once the approach proves reliable.
Looking to Use Predictive Analytics in Cybersecurity?
AI Superior can help with:
- evaluating security and log data
- building predictive models
- integrating models into existing systems
- improving detection over time
👉 Contact AI Superior to discuss your project, data, and implementation approach
Core Applications in Threat Prevention
Predictive analytics delivers value across multiple security domains. The most impactful applications include breach prediction, insider threat detection, vulnerability prioritization, and behavioral anomaly identification.
Breach prediction models analyze historical attack data to identify systems most likely to face intrusion attempts. These models consider factors like software versions, patch status, access patterns, and industry-specific threat trends. Security teams can then focus hardening efforts on the highest-risk assets.
Insider threat detection represents another critical use case. By establishing baseline patterns for user behavior—login times, data access volumes, typical file operations—analytics engines flag unusual activity that might indicate compromised credentials or malicious insiders.
Real-World Implementation Examples
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has integrated AI tools to spot anomalies in network data and enhance cyber defense capabilities. These applications demonstrate how government organizations leverage predictive capabilities to supplement traditional security controls.
| Application Area | Primary Benefit | Key Technique |
|---|---|---|
| Breach Prediction | Forecast attack likelihood | Risk scoring models |
| Insider Threats | Detect behavioral anomalies | User behavior analytics |
| Vulnerability Management | Prioritize patching efforts | Exploitability forecasting |
| Network Security | Identify traffic anomalies | Pattern recognition |
| Malware Detection | Spot zero-day threats | Unsupervised clustering |
Benefits That Actually Matter
Organizations adopting predictive analytics report several tangible improvements. The shift from reactive to proactive security reduces incident response costs by containing threats before they cause damage.
False positive reduction stands out as a major operational benefit. Traditional signature-based systems generate thousands of alerts daily, overwhelming security analysts with noise. Predictive models filter that stream by calculating probability scores, surfacing only high-confidence threats that warrant investigation.
Resource allocation becomes more strategic when teams know which vulnerabilities pose the greatest risk. Instead of patching everything equally or following arbitrary schedules, security professionals can prioritize based on actual exploitation likelihood.
Compliance requirements increasingly demand proactive monitoring. Predictive analytics supports audit requirements by demonstrating continuous risk assessment and documented threat mitigation efforts.
Implementation Challenges and Practical Considerations
Deploying predictive analytics isn’t plug-and-play. Organizations face several hurdles that require careful planning and realistic expectations.
- Data quality determines model effectiveness. Predictive algorithms need clean, comprehensive historical data to train accurately. Incomplete logs, inconsistent formatting, or gaps in event records undermine forecasting reliability. Most organizations need to invest months improving data collection practices before predictive models deliver value.
- Skilled personnel remain scarce. Effective implementation requires expertise spanning cybersecurity, data science, and statistics. Finding professionals who understand both threat landscapes and machine learning methodology proves difficult for many organizations.
- Model maintenance represents an ongoing commitment. Threat actors constantly evolve tactics, which means predictive models require regular retraining on fresh data. A model trained on 2024 attack patterns won’t accurately forecast 2026 threats without continuous updates.
- Integration complexity can derail projects. Predictive analytics platforms must ingest data from firewalls, SIEM systems, endpoint agents, and threat intelligence feeds. Connecting those disparate data sources and normalizing formats requires significant engineering effort.
The Role of Threat Intelligence Frameworks
Predictive analytics gains significant power when integrated with structured threat intelligence frameworks like MITRE ATT&CK. This globally-accessible knowledge base catalogs adversary tactics and techniques based on real-world observations, providing context that enhances predictive model accuracy.
Organizations can map their predictive alerts to specific ATT&CK techniques, helping analysts understand not just that an anomaly occurred, but which stage of an attack chain it represents. That context speeds response decisions and helps prioritize defensive measures.
MITRE’s threat modeling guidance demonstrates how to integrate ATT&CK into existing security methodologies. Detection strategies within the framework offer high-level approaches for identifying specific adversary techniques, serving as templates that predictive models can operationalize.
Looking Ahead: Future Developments
Generative AI represents the next frontier in predictive cybersecurity. Beyond pattern recognition, these systems can simulate attack scenarios, generate synthetic threat data for model training, and even predict novel attack vectors by extrapolating from known techniques.
The National Institute of Standards and Technology (NIST) continues developing frameworks for AI system security. Published guidance on securing AI systems and managing AI risks provides organizations with standards-based approaches to implementing predictive analytics while maintaining security and trustworthiness.
Cross-domain intelligence fusion will likely accelerate. Predictive models that incorporate threat data from multiple industries and geographic regions can identify emerging attack trends faster than siloed systems analyzing only organizational data.
Automated response capabilities are maturing. Current predictive systems flag threats for human review, but future implementations will increasingly trigger automated countermeasures—dynamic firewall rule updates, access revocations, or system isolations—based on high-confidence predictions.
Frequently Asked Questions
How accurate are predictive analytics models in cybersecurity?
Accuracy varies based on data quality, model sophistication, and threat type. Well-trained models can achieve significant accuracy for known attack patterns, though specific accuracy rates vary based on implementation and data quality. Zero-day exploits remain harder to forecast. The goal is probability assessment rather than perfect prediction—models calculate likelihood scores that help prioritize security efforts.
What’s the difference between predictive analytics and traditional threat detection?
Traditional detection identifies threats already present in systems using signature matching or rule-based alerts. Predictive analytics forecasts future threats by analyzing historical patterns and behavioral anomalies, enabling proactive defense before attacks materialize. Think of it as the difference between a smoke detector and a weather forecast.
Do small organizations benefit from predictive analytics or is it only for enterprises?
While large enterprises pioneered predictive security, cloud-based platforms now make these capabilities accessible to smaller organizations. Managed security service providers offer predictive analytics as a service, eliminating the need for in-house data science teams. Even modest implementations that prioritize vulnerability patching based on exploitability forecasts deliver meaningful risk reduction.
What data sources feed predictive cybersecurity models?
Effective models integrate multiple data streams: network traffic logs, authentication records, endpoint telemetry, threat intelligence feeds, vulnerability databases, and user behavior patterns. External sources like industry-specific threat reports and dark web monitoring also enhance predictions. The more diverse and comprehensive the data, the more accurate the forecasting.
How long does it take to implement predictive analytics in a security program?
Timeline depends on existing infrastructure and data maturity. Organizations with clean, centralized logging may pilot basic predictive capabilities relatively quickly. Comprehensive implementations typically require significant time to integrate data sources, tune models, and establish workflows. Data quality improvement often represents the longest phase.
Can predictive analytics replace human security analysts?
No. Predictive analytics augments human decision-making rather than replacing it. Models flag high-probability threats and prioritize alerts, but experienced analysts remain essential for interpreting context, investigating anomalies, and making nuanced response decisions. The technology eliminates repetitive triage work, freeing analysts to focus on complex investigations.
What are the main risks of relying on predictive models?
Over-reliance on predictions can create blind spots if models miss novel attack techniques. False negatives—threats the model fails to flag—pose serious risks. Model bias from unrepresentative training data can also skew predictions. Organizations should treat predictive analytics as one layer in defense-in-depth strategies, not a standalone solution.
Conclusion
Predictive analytics fundamentally changes how organizations approach cybersecurity. By shifting from reactive incident response to proactive threat forecasting, security teams can allocate resources more effectively, reduce false positives, and prevent breaches before they occur.
The technology isn’t a silver bullet. Successful implementation demands quality data, skilled personnel, continuous model maintenance, and realistic expectations about accuracy limitations. But for organizations willing to make that investment, predictive capabilities deliver measurable improvements in security posture.
As threat actors grow more sophisticated and attack surfaces expand, waiting for incidents before responding becomes increasingly untenable. Predictive analytics offers a path forward—one where defenders anticipate threats rather than chase them.
Start by assessing your current data collection practices and identifying gaps. Build foundational capabilities before pursuing advanced implementations. The shift to predictive security is a journey, not a destination, but each step forward strengthens defenses against tomorrow’s threats.
